Security

Accelerate secure coding with AI and real-time developer learning
July 15, 2025•
3 min read
Digital trust is the new currency
July 14, 2025•
4 min read
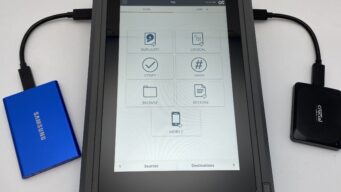
Speed, integrity, and confidence: Meet the new OpenText™ Forensic TX2 Imager
July 14, 2025•
3 min read

Secure AI development with OpenText: Protecting GenAI-enabled applications at scale
July 14, 2025•
2 min read

Enhance secure information management with DFIR
July 03, 2025•
5 min read

People, risk, and the modern CISO
June 17, 2025•
6 min read

Why CISOs are quietly becoming information architects
June 06, 2025•
3 min read

The future of cybersecurity: Insights from RSAC 2025
June 04, 2025•
5 min read

Identifying risks for an internal data breach within unstructured data
June 03, 2025•
3 min read

Why Managed Security Services are essential in today’s cyber landscape
May 29, 2025•
4 min read

