Bloomberg Businessweek’s story about hacked Super Micro server motherboards continues to reverberate around the tech echo chamber. You remember: the one about tiny spy chips in Apple and Amazon data centers, right?
“The Big Hack,” as the publication calls it, sets journalist against tech titan. The three companies are issuing ever-stronger denials, while Bloomberg’s editors doggedly stick to the story they’ve been working on for more than a year.
After three weeks, we’re still talking about it. And what does that tell you? In this week’s Security Blogwatch, we unpick, unwrap, and unwisely underline.
Your humble blogwatcher curated these bloggy bits for your entertainment. Not to mention: Turing, Tutte and Tunny …
Big story or bogus shenanigans?
What’s the craic? Duncan Riley drives in this summary—Apple, Amazon and Super Micro call on Bloomberg to retract:
The three major companies named in a Bloomberg report that claimed that their hardware had been infected with tiny … spy chips are calling on the news service to retract the story. … The report had been strongly denied by all involved previously but now [they] are calling upon Bloomberg to retract the story in its entirety.
…
Tim Cook led the charge [on] Oct. 19. … Amazon Web Services Inc. CEO Andy Jassy … joined the call [Monday], writing on Twitter that Tim Cook was right. … Supermicro CEO Charles Liang, the head of the company that is at the center of alleged … spying, was next to weigh in.
…
Bloomberg has yet to comment on the latest calls but doubled down on the story Oct. 9 by claiming that the same … spying devices had been found on servers used by a major U.S. telecommunication company. All four major U.S. telcos denied any knowledge.
But they would say that, wouldn’t they? John Paczkowski and Joseph Bernstein chat to Apple CEO Tim Cook:
There is no truth in their story about Apple. … They need to do the right thing and retract it.
…
I was involved in our response to this story from the beginning. … I personally talked to the Bloomberg reporters along with Bruce Sewell, who was then our general counsel. We were very clear with them that this did not happen, and answered all their questions.
…
Each time they brought this up to us, the story changed, and each time we investigated we found nothing. … We turned the company upside down. … Email searches, data center records, financial records, shipment records.
…
We really forensically whipped through the company to dig very deep and each time we came back to the same conclusion: This did not happen. There’s no truth to this.
And what of Amazon? AWS alpha Andy Jassy gets sassy: [You’re fired—Ed.]
Tim Cook is right. Bloomberg story is wrong about Amazon, too.
…
They offered no proof, story kept changing, and showed no interest in our answers unless we could validate their theories. Reporters got played or took liberties.
…
Bloomberg should retract.
But Bloomberg Businessweek sticks to its guns:
[Our] investigation is the result of more than a year of reporting, during which we conducted more than 100 interviews.
…
Seventeen individual sources, including government officials and insiders at the companies, confirmed the manipulation of hardware and other elements of the attacks.
…
We stand by our story and are confident in our reporting and sources.
Will no one rid Thomas Rid of this turbulent story? @RidT tweets:
Bloomberg's "big hack" story is the single biggest cockup in infosec reporting that I know of. That's quite a statement, mind you, for there have been many cockups.
…
Yes, a supply-chain hack is possible in theory. … Of course it is. The point is that there is NO EVIDENCE so far for an alleged operation that should by definition create hard evidence if it actually happened.
…
Bogus infosec stories turn into infosec zombies—you can't kill them. Because this field has been sick of FUD for years already. Because "fake news" has become a slur.
…
FACTS are an incredible treasure if you're working in science, in history, in intelligence, in law enforcement, in forensics, or investigative journalism—some of us obsess about the quality of evidence and tiny details all day long.
…
Admitting and correcting an error should really be an honor in professions that trade in facts. … So man up Bloomberg … and try to salvage your badly tarnished reputation in computer security reporting.
In a similar vein, here’s Robert Graham—@ErrataRob:
[This] is a great opportunity to talk about problems with journalism. … The technical details in Bloomberg's story … are garbled.
…
Something like what Bloomberg describes is certainly plausible, something exactly [like] what Bloomberg describes is impossible. [But] truth and near truth can be quite far apart, telling very different stories.
…
One [of] the justifications journalists use is that near truth is easier for their readers to understand. [But] if I as an expert can't figure out what actually happened, then I know that the average reader can't, either, no matter how much you've "simplified."
…
I have no trouble believing … at some point, that an intelligence organization subverted chips to hack BMC controllers in servers destined for specific customers. I'm sure our own government has done this at least once.
…
However, that doesn't mean the Bloomberg story is truthful. … This is why I trust the high-tech industry press so much more than the mainstream press.
Wait. Pause. It’s been three weeks already. This is Arts & Letters—@la__civetta:
[Bloomberg Businessweek editors still] stand by it. Wouldn't have published it if they didn't. … Which is what makes it interesting.
…
Fully understand the company, those in the profession, [and] what a year of research means. This is not Fox. There is something strange here. … That is what makes it truly curious.
…
Not speaking about corroborating evidence doesn’t mean there isn’t any. They would only base a story on indisputable evidence. Unless high level govt departments were intentionally lying to them?
Kieren McCarthy tries to make sense of it all:
The article has been strongly denied by the three main companies involved. … [T]hese statements will have gone through layers of lawyers to make sure they do not open these publicly traded corporations to lawsuits. … Similarly, Bloomberg employs veteran reporters and layers of editors … and has a zero tolerance for inaccuracies.
…
The Bloomberg article is not particularly technical [but] from what we can tell, the spy chip … could have been placed electrically between the baseboard management controller (BMC) and … the BMC's firmware … allowing its masters to control the … server motherboard. … This explanation seemingly passes the sniff test: it fits what we know of US intelligence agencies' investigative approaches … and how the Chinese government works.
…
The denials are far more precise and concrete than typical non-denial denials. … Typical giveaways are when such statements are over-the-top … or when a denial is either overly specific … or is unnecessarily vague. … There are examples of those in the various statements put out by the companies.
…
So we have: two Amazon employees, three Apple employees, six intelligence agencies officials, six other people that Bloomberg says confirmed various different aspects of the story. … But is it possible there was all a big misunderstanding somewhere down the line? [Or did they get] 90 per cent of the way there and Apple and Amazon are carefully using the last 10 per cent to issue careful denials?
So jezwel thinks a bit further:
Does national security (NSA) override the SEC? If so, it doesn't matter that the companies might be lying about these chips—they won't be prosecuted as that would expose what's going on.
And Aighearach lays out the options:
News flash: We have no idea if the NSA modifies actual hardware. As far as we know, they do, and they were the ones who modified the hardware in this story.
Or they weren't, but they want people to think that they do.
Or they don't, but they're worried somebody will leak that they don't, so they leaked a fake story that they did.
Or they do, and they were worried about a leak, so they leaked that they don't.
Or they do, and they were worried about a leak, so they leaked that they do, so that they can control the story. (Like the Air Force did with the "weather balloon" when their experimental aircraft crashed off-base.)
But we could try to follow the money, thinks ShanghaiBill:
The agencies would get major budget boosts if they can show that the Chinese infiltrated all of these companies. They have a strong vested interest in making China look like a powerful and dangerous boogeyman.
Meanwhile, rtb61 takes a deep breath:
Public company, short the stocks, spread a story—voila! Big profits to be made.
It's all part of the corporate wars, using various criminal methods and attack and destroy other corporations, spreading misinformation just a minor part, computer hacking of all kinds, corrupting staff in competing companies and you can expect targeted assassination to follow.
The moral of the story? There’s something going on, but what? This is at least a reminder that state actors are powerful, and wield that power in many ways.
And finally …
You have been reading Security Blogwatch by Richi Jennings. Richi curates the best bloggy bits, finest forums, and weirdest websites … so you don’t have to. Hate mail may be directed to @RiCHi or sbw@richi.uk. Ask your doctor before reading. Your mileage may vary. E&OE.
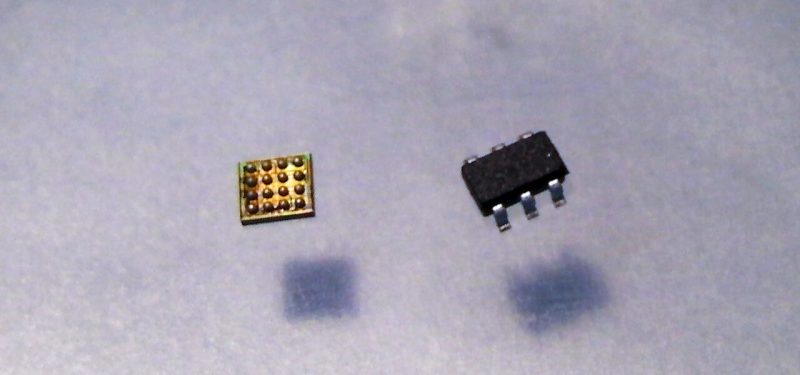
Image source: Kohei Matsumura (cc:by)
Keep learning
Get up to speed on unstructured data security with TechBeacon's Guide. Plus: Get the Forrester Wave for Unstructured Data Security Flatforms, Q2 2021.
Join this discussion about how to break the Ground Hog Day repetition with better data management capabilities.
Learn how to accelerate your analytics securely into the cloud in this Webinar.
Find out more about cloud security and privacy, and selecting the right encryption and key management in TechBeacon's Guide.
Learn to appreciate the art of data protection and go behind the privacy shield in this Webinar.
Dive into the new laws with TechBeacon's guide to GDPR and CCPA.